SSL vs TLS – What’s the Difference?
SSL vs TLS certificate is a cryptographic protocol that encrypts data being exchanged/transferred between the web server and a user. Internet security is a jargon-filled world. For a newbie, it is a nightmare to make sense of these terms and how they work together.
It takes a lot of prodding to understand how they work and how they are different from one another. If you have been reading about SSL recently, you would have stumbled across TLS as well. SSL refers to Secure Sockets Layer whereas TLS refers to Transport Layer Security. Basically, they are one and the same, but, entirely different.
How similar both are? SSL and TLS are cryptographic protocols that authenticate data transfer between servers, systems, applications, and users. For example, a cryptographic protocol encrypts the data that is exchanged between a web server and a user. SSL was the first kind of cryptographic protocol. TLS on the other hand was a recently upgraded version of SSL.
A Brief History of SSL and TLS
SSL vs TLS are both cryptographic protocols that provide authentication and data encryption between servers, machines, and applications operating over a network (e.g. a client connecting to a web server). In reality, SSL is only about 25 years old. But in internet years, that’s ancient. The first iteration of SSL, version 1.0, was first developed in 1995 by Netscape but was never released because it was riddled with serious security flaws. SSL 2.0 wasn’t a whole lot better, so just a year later SSL 3.0 was released. Again, it had serious security flaws.
At that point, the guys at Consensus Development took a crack at it and developed TLS 1.0. TLS 1.0 was incredibly similar to SSL 3.0 – in fact, it was based on it – but still different enough to require a downgrade before SSL 3.0 could be used. As the creators of the TLS protocol wrote: “The differences between this protocol and SSL 3.0 are not dramatic, but they are significant enough that TLS 1.0 and SSL 3.0 do not interoperate.”
Downgrading to SSL 3.0 was still dangerous, though, given its known, exploitable vulnerabilities. All an attacker needed to do to target a website was downgraded the protocol to SSL 3.0. Hence, the birth of downgrade attacks. That ended up being the nail in the coffin for TLS 1.0.
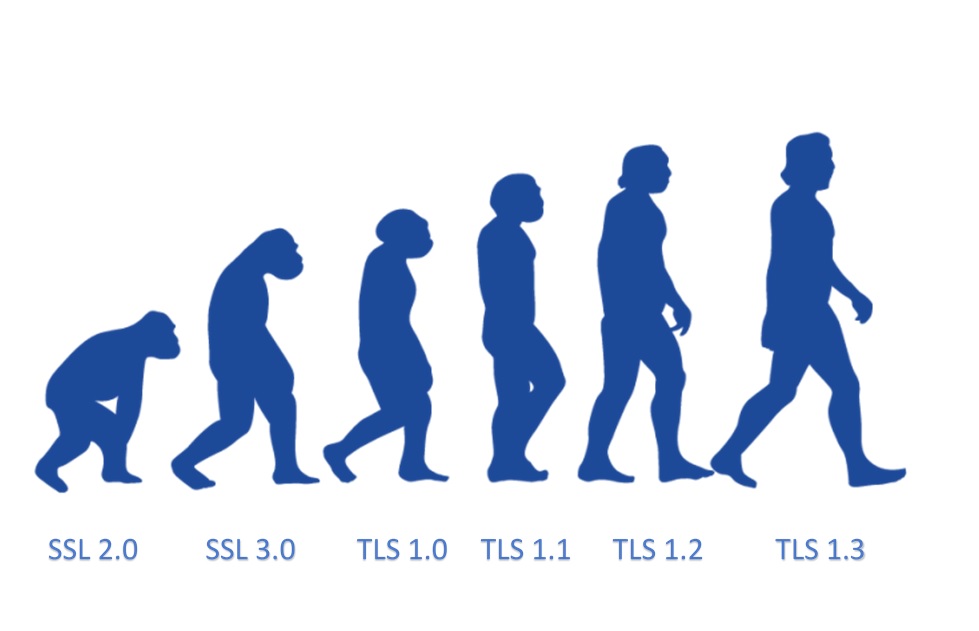
TLS 1.1 came out seven years later in 2006, replaced by TLS 1.2 in 2008. That hurt TLS 1.1 adoption as many websites simply upgraded from 1.0 to TLS 1.2. We are now at TLS 1.3, which was finalized in 2018 after 11 years and nearly 30 IETF drafts.
TLS 1.3 makes significant improvements over its predecessors and right now major players around the internet are pushing for its proliferation. Microsoft, Apple, Google, Mozilla, and Cloudflare all announced plans to deprecate both TLS 1.0 and TLS 1.1 in January 2020, making TLS 1.2 and TLS 1.3 the only game in town.
At any rate, we’ve been using TLS for the past couple of decades. At this point, if you’re still using SSL you’re years behind, metaphorically living in a forlorn era where people still use phone lines to dial on to the internet.
SSL vs TLS: The Key Differences Between These Protocols
However, the differences between SSL and TLS are very minor. In fact, only a technical person will be able to spot the differences. The notable differences include:
Cipher suites
SSL protocol offers support for the Fortezza cipher suite. TLS does not offer support. TLS follows a better standardization process that makes defining new cipher suites easier like RC4, Triple DES, AES, IDEA, etc.
Alert messages
SSL has the “No certificate” alert message. TLS protocol removes the alert message and replaces it with several other alert messages.
Record Protocol
SSL uses Message Authentication Code (MAC) after encrypting each message while TLS on the other hand uses HMAC — a hash-based message authentication code after each message encryption.
Handshake process
In SSL, the hash calculation also comprises the master secret and pad while in TLS, the hashes are calculated over a handshake message.
Message Authentication
SSL message authentication adjoins the key details and application data in an ad-hoc way while the TLS version relies on HMAC Hash-based Message Authentication Code.
These are the essential differences between an SSL vs TLS certificate. As I mentioned before, it takes a trained eye to understand the differences.

SSL vs TLS: Do you Need to Replace Your SSL Certificates with TLS Certificates?
Well, of course not. That’s because both “SSL certificate” and “TLS certificate” essentially mean the same thing: They’re both X.509 digital certificates that help to authenticate the server and facilitate the handshake process to create a secure connection.
Some people call them “SSL certificates,” while others refer to them as “TLS certificates.” The name doesn’t matter much because a certificate isn’t the same thing as the protocol. Whatever you call them, what matters is the protocol that they operate on. These protocols are determined by your server configuration, not by the digital certificates. So, you must make sure that your web server supports the latest TLS protocols.
Similarly, you must also enable server support for higher encryption strength. Why? Because encryption strength isn’t based on the certificate — it’s dependent on the configuration of the server and client.
Having said all this, these certificates are mostly called “SSL certificates.” Many people have started using the term “TLS certificate,” but you don’t need to get confused between them as both mean the same thing.
Summary
To sum everything up, TLS and SSL are both protocols to authenticate and encrypt the transfer of data on the Internet. The two are tightly linked and TLS is really just the more modern, secure version of SSL. While SSL is still the dominant term on the Internet, most people really mean TLS when they say SSL, because both public versions of SSL are not secure and have long since been deprecated.