Sandboxing: Definition
Sandboxing comes under the cyber security section, which creates an isolated environment within the network that mimics the end-user operating environment. It is always safe to execute with a suspicious code where no risk is included. It will also host the device.
What is Sandboxing?
Sandboxing is a cyber security practice where you run code, observe and analyze, and code in a safe, isolated environment on a network that mimics end-user operating environments. It is designed to prevent threats from getting on the network and is frequently used to inspect untested or untrusted code. It keeps the code relegated to a test environment so it doesn’t infect or cause damage to the host machine or operating system.
As the name suggests, this isolated test environment functions as a kind of “sandbox,” where you can play with different variables and see how the program works. This is also a safe space, where it can’t actively harm your host devices if something goes wrong.
Why Sandboxing is important
The quantity and effectiveness of zero-day threats are constantly growing, so you must have a strategy to protect your data and programs from threats that evade traditional email, malware, and virus filters. Sandboxing is among the most foolproof tools for staying one step ahead of hackers. There are cloud-based sandboxing solutions available that provide effective protection without suffering the common drawbacks of degrading your network performance or being easily evaded by clever hackers.
How does it work?
It is conducted by setting up an isolated test area or a “sandbox” that is ingested with malicious code or malware. The resulting behavior patterns are then observed and are classified as either “safe” or “unsafe” after the mock test is completed.
While most legacy security models operate on a reactive approach, sandboxing works proactively by observing both old and new patterns alike. This adds an extra layer of security and protects against many vulnerabilities like zero-day and hidden stealth attacks.
Both the cyber security and software development worlds use it as a standard practice but ensuring a fully isolated sandbox is more important for security purposes because the nature of malware is to continuously and aggressively scan networks for vulnerabilities.
The benefits of Sandboxing
- Do not risk your host devices or operating systems. The main advantage of sandboxing is that it prevents your host devices and operating systems from being exposed to potential threats.
- Evaluate potentially malicious software for threats. If you’re working with new vendors or untrusted software sources, you can test new software for threats before implementing it.
- Test software changes before they go live. If you’re developing new code, you can use sandboxing to evaluate it for potential vulnerabilities before it goes live.
- Quarantine zero-day threats. With sandboxing, you can quarantine and eliminate zero-day threats.
- Complement other security strategies. Sandboxing functions as a complementary strategy to your other security products and policies, providing you with even more protection.
What are Sandbox environments?
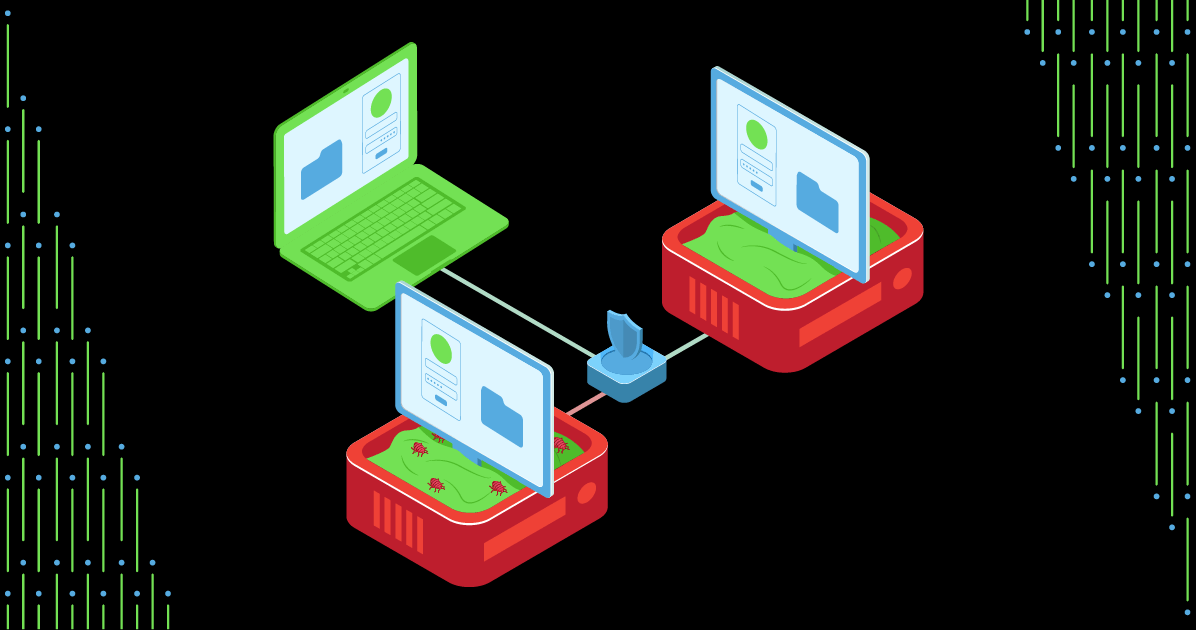
A sandbox environment is a safe testing ground that isolates code that needs to be tested or experiments that have the potential to affect other aspects of your network.
Sandboxing can take several different forms. Even though some companies use it only for testing, it is also a valuable tool for several other important objectives. One such objective is project integration. Integrating more than one build or aspect of a project can be a challenge. However, with it, you can check for compatibility to make sure the solution is being properly developed.
Sandboxing also allows your clients and customers to use new products and features. For example, you can execute sales demonstrations within a sandboxed environment. These can include videos and other multimedia, and with a properly equipped sandbox, the customer can take away an experience identical to what they would have when connected to your actual system. It allows your company to interactively engage with both new clients and customers already in your portfolio. They can try out your software at their own pace, no matter where they are.
You can also perform quality assurance (QA) testing within a sandbox environment. Using sandbox software to optimize your solution enables you to isolate problematic elements of the code and then troubleshoot them. It protects the rest of your system while giving you the chance to execute code in an ecosystem much like what the end-user would experience.
Example of using Sandbox
Users can use the sandbox to isolate the code execution, and in any situation, you can use this software. Here you can get a few specific examples those are below:
- Web browsers: A correct web browser can run itself inside the sandbox. This is a website that can exploit the vulnerability in the web browser. If you use this, you will have less damage.
- Software protection: Few tools allow users to run untrusted software but cannot access private data or harm the device.
- Security research: Mainly, the information security professional uses the sandbox to detect malicious code. Security tools also can visit the website so that they can monitor the changes and extra things that need to be installed or not.
- Virtualization: The virtual machine is also one type of sandbox that examines the suspicious program.

Conclusion
Sandbox provides developers with a safe environment where they have unfinished software programs. If we talk about the multiple layers, then sandboxes are very effective and combined with the other security measures.